A A Randomly Generated 256-bit Binary Key
Ways to generate symmetric and asymmetric keys. Ask Question. To generate such a key, use OpenSSL as: openssl rand 16 myaes.key AES-256 expects a key of 256 bit, 32 byte. To generate such a key, use. As their name state they both are pseudo random number generator, meaning they both are deterministic algorithms which, given the same. WARNING: do not actually execute this. You will not be able to recover the files. This is intended to encrypt every bit of data in a unix filesystem using 256-bit AES with a self-destructing, randomly generated key. I'm trying to create a strong key for encrypting some data using AES-256 for fun and practice. For my own practice, I want to make this as strong as possible, I don't care how long it takes to complete. I got some advice from 1Password white paper and therefore I want to use 2 secret keys. The master password and a random generated 32-byte string.
- Openssl Generate 256 Bit Key
- A A Randomly Generated 256-bit Binary Key Sheet
- Random 256 Bit Key Generator
The binary log master key is used to encrypt each new log file's file password, which is a randomly generated 32-byte file password specific to the log file that is used to encrypt the file data. The file password is encrypted using AES-CBC (AES Cipher Block Chaining mode) with the 256-bit binary log encryption key and a random initialization vector (IV), and is stored in the log file's file header. In python i'm using the Crypto package to generate a random number of length 256 bit. The function for doing so is import Crypto.Random.random as rand key = rand.getrandbits(256) This gives Stack Overflow.
The binary log encryption keys used to encrypt the file passwords for the log files are 256-bit keys that are generated specifically for each MySQL server instance using MySQL Server's keyring service (see Section 6.4.4, “The MySQL Keyring”). The keyring service handles the creation, retrieval, and deletion of the binary log encryption keys. A server instance only creates and removes keys generated for itself, but it can read keys generated for other instances if they are stored in the keyring, as in the case of a server instance that has been cloned by file copying.
The binary log encryption keys for a MySQL server instance must be included in your backup and recovery procedures, because if the keys required to decrypt the file passwords for current and retained binary log files or relay log files are lost, it might not be possible to start the server.
The format of binary log encryption keys in the keyring is as follows:
For example:

Openssl Generate 256 Bit Key
{UUID} is the true UUID generated by the MySQL server (the value of the server_uuid system variable). {SEQ_NO} is the sequence number for the binary log encryption key, which is incremented by 1 for each new key that is generated on the server.
A A Randomly Generated 256-bit Binary Key Sheet
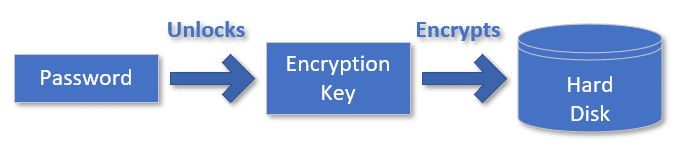
The binary log encryption key that is currently in use on the server is called the binary log master key. The sequence number for the current binary log master key is stored in the keyring. The binary log master key is used to encrypt each new log file's file password, which is a randomly generated 32-byte file password specific to the log file that is used to encrypt the file data. The file password is encrypted using AES-CBC (AES Cipher Block Chaining mode) with the 256-bit binary log encryption key and a random initialization vector (IV), and is stored in the log file's file header. The file data is encrypted using AES-CTR (AES Counter mode) with a 256-bit key generated from the file password and a nonce also generated from the file password. It is technically possible to decrypt an encrypted file offline, if the binary log encryption key used to encrypt the file password is known, by using tools available in the OpenSSL cryptography toolkit.
Random 256 Bit Key Generator
If you use file copying to clone a MySQL server instance that has encryption active so its binary log files and relay log files are encrypted, ensure that the keyring is also copied, so that the clone server can read the binary log encryption keys from the source server. When encryption is activated on the clone server (either at startup or subsequently), the clone server recognizes that the binary log encryption keys used with the copied files include the generated UUID of the source server. It automatically generates a new binary log encryption key using its own generated UUID, and uses this to encrypt the file passwords for subsequent binary log files and relay log files. The copied files continue to be read using the source server's keys.